Please note: The bug bounty program ended on August 31, 2023. Thank you for all your feedback!
Since Ruby.Exchange launched in beta back in June, our community has proven extremely valuable in hunting down bugs and helping us refine the site's UX. A big "thank you" to all who have contributed insights and suggestions!
As we move into the next stage and start listing SKALE ecosystem tokens, we're launching a formal bug bounty campaign to reward those who help us to find and fix any further bugs that may currently exist, or be introduced by new functionality. If you identify a vulnerability or a UX issue, you'll receive a stack of $RUBY as a token of our appreciation!
Bounty Criteria
Ruby's bounty program applies to our core repository: https://github.com/RubyExchange.
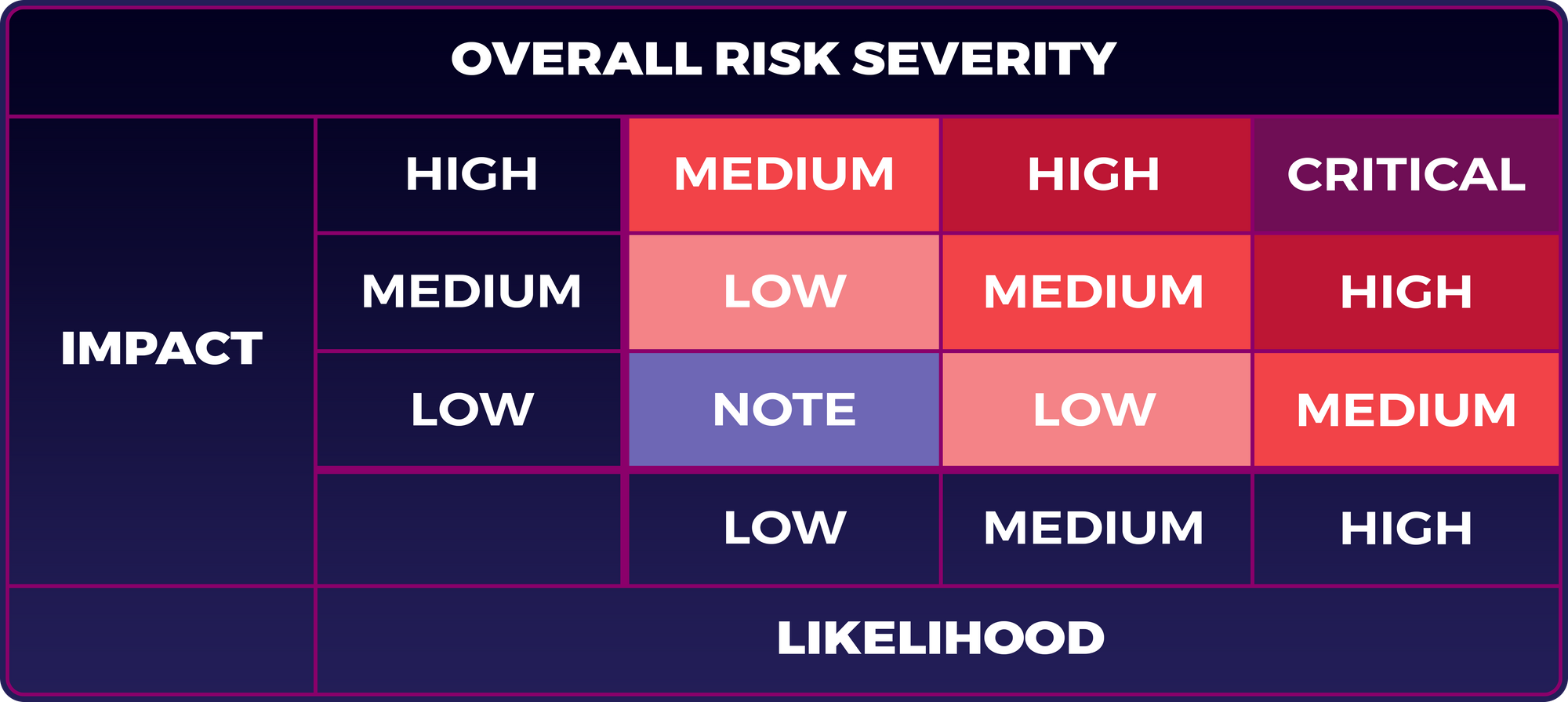
Like other bounty programs, we will classify any bugs by their severity, and reward them accordingly. The severity of a bug depends on both its potential impact, and how likely or possible that exploit is.
For example, an exploit that could result in loss of user funds in theory, but is virtually impossible to carry out in practice, might not receive as high a rating as one that allowed a hacker to cause less disruption with relative ease. We have adopted the OWASP risk rating model:
Vulnerabilities found in each tier will receive a bounty of $RUBY tokens, up to a maximum dollar-equivalent amount:
- Critical: Up to $10,000
- High: Up to $5,000
- Medium: Up to $2,000
- Low: Up to $1,000
Additional Guidelines
Several other factors will inform the level of reward offered to bug finders, including:
- Quality of report. The more information you can give about the vulnerability, and the more clearly this is presented, the better.
- Reproducibility. Please provide the precise steps required to reproduce the bug, since we'll need to verify it exists and determine what is causing it.
- Solutions. If you can offer suggestions for how to fix the vulnerability, your submission is likely to receive a larger reward.
While the severity allocated to each bug and the bounty payment will be informed by the risk rating model and these guidelines, rewards will ultimately be at the discretion of the dev team.
Bounty Program Rules
We will only reward responsible investigation and submission of any vulnerabilities discovered. Failure to maintain best practices will lead to disqualification. For example:
- Do not target other users, damage our systems, or attempt to delete data.
- Only vulnerabilities specific to Ruby are eligible. Social engineering, phishing, DDoS attacks, etc, do not qualify.
- Public disclosure of vulnerabilities will result in disqualification for any rewards.
- Bugs must be disclosed only to the Ruby team, and a reasonable interval should be left before sharing details with other parties.
- Any bug that has already been submitted, or that is already known to the dev team, whether or not this has been made public, will not be eligible for rewards.
- The level of rewards paid out for finding each bug will be decided by the dev team, on a case-by-case basis.
How To Submit Your Bug Report
To submit a bug report, email hello@ruby.exchange. Please include as much information as you can about the vulnerability you have discovered, its real or potential impact on users, the correct steps required to reproduce it and, if possible, your suggestions for addressing the problem.
For minor bugs, following up emails, or discussing existing bugs, you can start a new topic in the #bugs channel of the Ruby Discord.
Follow us on Twitter, join the conversation on Discord, and subscribe to the Ruby blog for regular updates.






